- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Is there a limit on the number of selected or ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is there a limit on the number of selected or interesting fields in Splunk?
Hi,
I have a log statement with almost 100 fields. When searched, it doesn't show all the fields in Selected fields nor in All fields tab. Is there a limitation for the number of fields in Splunk? If so, where do I change it?
I used the table command to make sure the missing fields are there, it's just not showing in the panel to the left.
Thanks.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check the answer by veganjay here: https://answers.splunk.com/answers/129773/advice-for-when-you-have-more-than-100-automatically-extra...
It worked for me.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
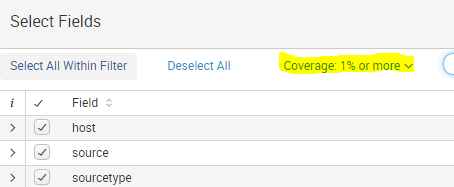
Jkat54, I've the same settings. The coverage is 1% or more.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Change it to All Fields.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also be sure you're searching in verbose mode.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, I tried it , but no luck. It doesn't show all the fields.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
But if I pipe
| fields abc then abc is showed in the fields list. But without that it doesn't show.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does it show in the fields picker if you change from 1% coverage to show all fields and then type the field name into the seacb bar in the fields picker? If so, just select the fields you want to see by default and they'll always be selected for your user when you're in that app context.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
NO, It doesn't show even if I change the coverage
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I believe the other thing it does which may be causing the issue, is it only samples a certain number of events. I believe the limit is set under [associate] in limits.conf but i'm not 100% sure. I recommend opening a support case to get a definitive answer.