- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Field shown by extraction of other field, but ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Why the field is shown by extraction of another field but not found by search?
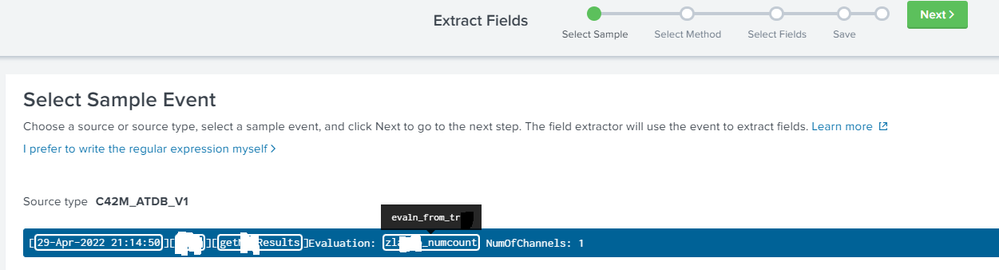
Hi, as I create an extraction field with regex, the field match is shown correct. I can check the regex on https://regex101.com/. The field is shown in raw events, if I tray to define next field
But in search the field is not found.
Field extraction regex: (?<=Evaluation: )(?P<evaln_from_tr>.*)(?= NumOfChannels)
Sample log line: [30-Apr-2022 05:52:40][XXX][getResults]Evaluation: zl_numcount NumOfChannels: 1
Permissions: Everybody read and write
Verbose mode search without a new field: index=XXX sourcetype=XXX host=XXX source="XXX.txt" method=geResults "* NumOfChannels: *"
found 1485 events like example, with different names.
Verbose mode search with a new field: index=XXX sourcetype=XXX host=XXX source="XXX.txt" method=geResults evaln_from_tr="*" "* NumOfChannels: *"
found 0 events!
Why the field is shown by extraction of another field but not found by search?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The expressions generated by the Field Extraction wizard aren't the greatest. Also, based on problems reported here, lookbehind and lookahead operators seem to be an issue.
Try this simpler regex:
Evaluation: (?P<evaln_from_tr>\S*)If this reply helps you, Karma would be appreciated.